Hardentools is designed to harden your machine's overall security via the disabling of multiple Windows, Office, and Acrobat Reader features, including ActiveX, autorun, autoplay, and macros.
Hardentools is designed to harden your machine's overall security via the disabling of multiple Windows, Office, and Acrobat Reader features, including ActiveX, autorun, autoplay, and macros.
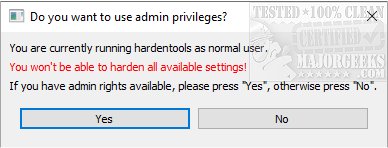
Hardentools is a straightforward application intended for users that want to increase Windows security in the most straightforward way possible. Hardentools can disable several system tools with a single click, which are generally of no real use to the casual user but can potentially leave a PC vulnerable to malware attacks.
These features, commonly thought for enterprise customers, are generally useless to regular users and can pose a danger as attackers commonly abuse them to execute malicious code on a victim's computer. This tool intends to reduce the attack surface by disabling the low-hanging fruit simply. Hardentools are designed for individuals at risk who might want an extra security level at the price of some usability. It is not intended for corporate environments.
Bear in mind, after running Hardentools, you won't be able, for example, to do complex calculations with Microsoft Office Excel or use the Command-line terminal, but those are pretty much the only considerable "downsides" of having a slightly safer Windows environment. Before deciding to use it, make sure you read this document thoroughly and understand that, yes, something might break. If you experience malfunctions due to the modifications implemented by this tool, please do let us know.
MajorGeeks recommends creating a restore point just in case, as stated above, Hardentools breaks something.
WARNING: This tool disables several features in Microsoft Office, Adobe Reader, and Windows, which may cause malfunctions to specific applications. Use this at your own risk.
Disabled Features:
Generic Windows Features
Disable Windows Script Host. Windows Script Host allows the execution of VBScript and Javascript files on Windows operating systems. This is very commonly used by regular malware (such as ransomware) as well as targeted malware.
Disabling AutoRun and AutoPlay. Disables AutoRun / AutoPlay for all devices. For example, this should prevent applications from automatically executing when you plug a USB stick into your computer.
Disables powershell.exe, powershell_ise.exe, and cmd.exe execution via Windows Explorer. You will not be able to use the terminal, and it should prevent the use of PowerShell by malicious code trying to infect the system.
Sets User Account Control (UAC) to always ask for permission (even on configuration changes only) and to use "secure desktop."
Disable file extensions mainly used for malicious purposes. Disables the ".hta", ".js", ".JSE", ".WSH",."WSF", ".scf", ".scr", ".vbs", ".vbe" and ".pif" file extensions for the current user (and for system-wide defaults, which is only relevant for newly created users).
Shows file extensions and hidden files in explorer.
Windows Defender Attack Surface Reduction (ASR). Enables various remediations using ASR starting with Windows 10 / 1709 (Block executable content from email client and webmail, Block Office applications from creating child processes, Block Office applications from creating executable content & from injecting code into other processes, Block JavaScript or VBScript from launching downloaded executable content, Block execution of potentially obfuscated scripts, Block Win32 API calls from Office macro). Needs the following prerequisites to work: (1) Windows 10 version >= 1709, (2) You are using Windows Defender Antivirus as the sole antivirus protection app. (3) Real-time protection is enabled in Windows Defender.
Microsoft Office
Disable Macros. Microsoft Office users sometimes use macros for scripting and automating certain activities, especially calculations with Microsoft Excel. However, macros are currently a security plague, and they are widely used as a vehicle for compromise. With Hardentools, macros are disabled, and the "Enable this Content" notification is disabled, too, to prevent users from being tricked.
Disable OLE object execution. Microsoft Office applications can embed so-called "OLE objects" and execute them, at times also automatically (for example, through PowerPoint animations). Windows executables, such as spyware, can also be embedded and executed as an object. This is also a security disaster that we repeatedly observed, particularly in attacks against activists in repressed regions. Hardentools entirely disables this functionality.
Disabling ActiveX. Disables ActiveX Controls for all Office applications.
Disable DDE. Disables DDE for Word and Excel
Acrobat Reader
Disable JavaScript in PDF documents. Acrobat Reader allows executing JavaScript code from within PDF documents. This is widely abused for exploitation and malicious activity.
Disable execution of objects embedded in PDF documents. Acrobat Reader also allows the execution of embedded objects by opening them. This would normally raise a security alert, but given that legitimate uses are rare and limited, Hardentools disables this.
Switch on the Protected Mode (enabled by default in current versions)
Switch on Protected View for all files from untrusted sources
Switch on Enhanced Security (enabled by default in current versions)
Similar:
How to Disable All Advertising and Sponsored Apps in Windows 10
How to Turn Diagnostic Data Settings on or off in Windows 10
How to Disable Windows 10 Activity History Permanently
How to Disable Advertising ID for Relevant Ads in Windows 10
How to Disable App Suggestions and Advertising in the Start Menu
Download