Chainsaw allows advanced users to search and hunt through Windows Event Logs rapidly.
Chainsaw allows advanced users to search and hunt through Windows Event Logs rapidly.
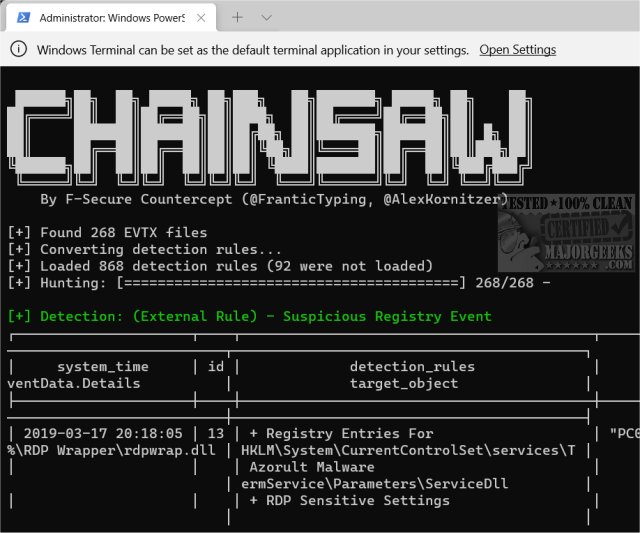
Chainsaw provides a powerful ‘first-response’ capability to identify threats within Windows event logs quickly. It offers a generic and fast method of searching through event logs for keywords and identifying threats using built-in detection logic and support for Sigma detection rules.
Features:
Search and extract event log records by event IDs, string matching, and regex patterns
Hunt for threats using Sigma detection rules and custom built-in detection logic
Lightning fast, written in rust, wrapping the EVTX parser library by OBenamram
Document tagging (detection logic matching) provided by the TAU Engine Library
Output in an ASCII table format, CSV format, or JSON format
Chainsaw is designed for advanced users who are comfortable using the Command Prompt. Chainsaw would be most useful for technicians, administrators, or IT.
If you want to see how to program looks, run the following command from the folder you extracted the files to:
./chainsaw hunt evtx_attack_samples/ --rules sigma_rules/ --mapping mapping_files/sigma-mapping.yml
Similar:
How to Clear All Event Logs in Event Viewer in Windows
How to Read the Event Viewer Log for Check Disk
Download